PlayStation hacker extraordinaire CTurt has a unpatched exploit for the PS4 and PS5, using the integrated PS2 emulator as the access point. As it stands, the hacker explains that the vulnerability would allow tinkerers to: run illegal PS2 games on the PS4/PS5 (and one can assume, PS2 homebrews). But he too promises more to come, especially PS4 native homebrew performance (PS4 user country).
The exploit, nicknamed mast1c0re, was disclosed to Sony by CTurt a year ago, but the developer was only now allowed to disclose it publicly. Nevertheless, according to the hacker, the exploit has not been patched, meaning it was recently released PS4 Firmware 10.00 and PS5 Firmware 6.00 are apparently vulnerable.
CTurt sent details of the exploit to PlayStation a year ago, but was only now allowed to make it public
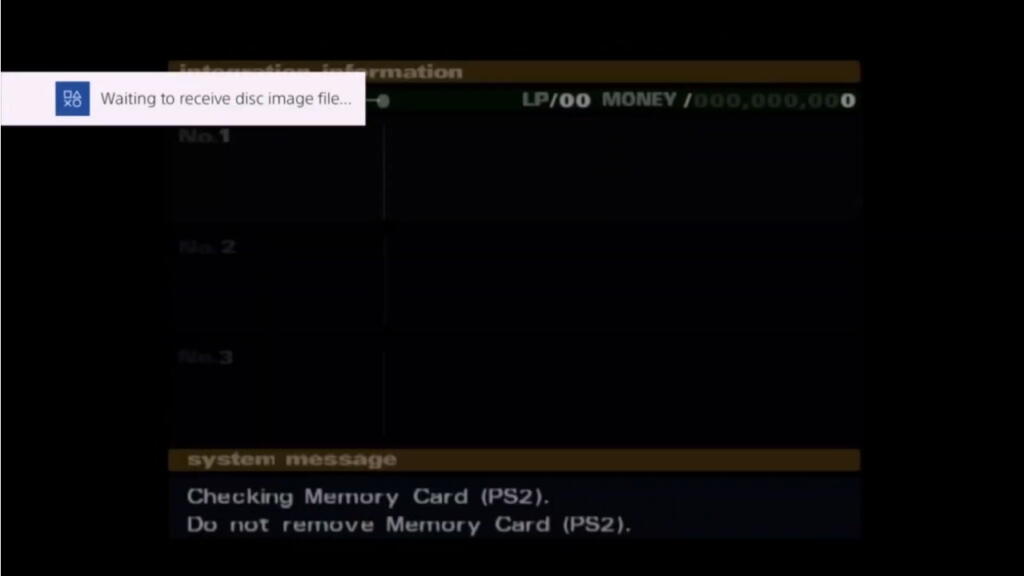
CTurt shared a full description of the exploit, as well as a video showing the exploit used to load another PS2 game from the emulator process. (writing and video links below)
mast1c0re – What is the PS4/PS5 userland hack about?
Hacking a console typically requires two levels of exploits: an access point that you can access within the limited limits you have as a console user, and a privilege escalation exploit (jailbreak). In practice, it can get much more complicated than that on modern systems with many other security measures to beat (ASLR, DEP, …), but the basic idea is always: entry point, then privilege escalation.
In this case, the mast1c0re exploit, as described in CTurt’s first document, is the starting point: taking advantage of the fact that the PS4 and PS5 can run PS2 games within an integrated emulator, and using existing PS2 exploits, is it possible to use the PS2 emulator on the PS4 and PS5 as an access point, via gamesave exploits.
This is a significantly different approach than using Webkit vulnerabilities, something that has historically been the main entry point for PS4 exploits. But for folks who’ve been in the hacking world for a while, this is a throwback to the good old days: the savegame used by PSP exploits a lot as a gateway to exploits, and closer to what’s accomplished here, the PS Vita also used the same. PSP exploits to provide limited hacking support, especially to enable PSP Homebrew in the early days.
mast1c0re – PS4 userland homebrew next?
In the current state of his explanation, Cturt describes that the hack allows for arbitrary execution within the PS2 emulator. In other words, it is possible to run PS2 games and PS2 homebrew on a PS4 (or PS5) through this hack. This is very similar to what VHBL allowed in the PSVita days (PSP Homebrew within the PS Vita’s PSP emulator).
But he promises there’s more to come in a “part 2” of his article, which is a (userland) PS4 homebrew environment. That aspect would require additional exploits to escape the PS2 environment and peel off one layer to get to the original PS4 level. How the hacker did this remains to be seen.
mast1c0re – What is the status right now and what should I do?
CTurt claims that the vulnerability is essentially “unpatchable”. As long as exploitable PS2 games are available for download, it should be possible to take advantage of this particular vulnerability. He states that he disclosed the vulnerability to Sony more than a year ago and that they have decided not to patch it.
Assuming this exploit leads to user-friendly releases (no doubt it will), it looks like a cat-and-mouse game could ensue between PlayStation and hackers, just like in the VHBL days: a new exploitable PS2 is coming. game found/announced, people are rushing to buy and download it before Sony removes it (temporarily?) from PSN. Rinse and repeat.
The game that Cturt has used for his ongoing work is OKAGE: Shadow King, an exploitable PS2 game. utilities before you rush to buy the game, the devil is in the details and there are a few things to understand:
- This game has been announced as leading to an exploit and is still available on PSN at the time of writing. How long it will stay on the PSN before Sony pulls it out is anyone’s guess. Could be today, could be next week, could never be. Once pulled, this opportunity is gone, but it’s likely other exploitable games will be revealed in the future.
- Technically nothing has been released yet. There is a non-zero possibility that this could lead to nothing useful for the end user
- What is currently being announced is PS2 homebrew and possibly PS4 Homebrew.
- Nothing about a PS4 full jailbreak, which requires a privilege escalation exploit (kernel exploit). Specifically, this means no PS4 piracy
- While CTurt says the PS2 exploit is basically unpatchable, the next level (PS4 user country) could be. There are actually rumors that a PS4 firmware 10.1 is coming soon, and that may have to do with what CTurt will reveal next (mast1c0re part 2)
- While CTurt lists the PS5 as vulnerable, it appears that much of its work is focused on the PS4. PS5 compatibility may only be theoretical at this point, especially for end users.
- Creating the correct PS2 savegame for your PS4 console requires a way to encrypt the savegame for your specific PSN ID. This means that someone with an already hacked PS4, or more advanced resources, should do it for you! While it sounds very likely that the community can provide services for that, it’s not as simple as your typical hack. Specific of CTurt: “Using one of these exploits, a PS4 save file containing the manufactured PS2 memory card can be encrypted and signed for any PSN ID by anyone with a hacked PS4 on any firmware (or just a PC if they have the decrypted SAMU keys), and then imported to the target PS4/PS5 using the USB storage import function in Settings.
Understand from the above that the game costs $10. For some, this might be a lot of money for something with no warranty. Don’t jump the gun and buy a PS2 game expecting something it isn’t.
mast1c0re – More details
For more details on the vulnerability, see CTurt’s description and the video below.
Stay tuned here on wololo.net, as there will surely be rapid developments in this area!
Source: CTurt
0 Comments